Save & Secure
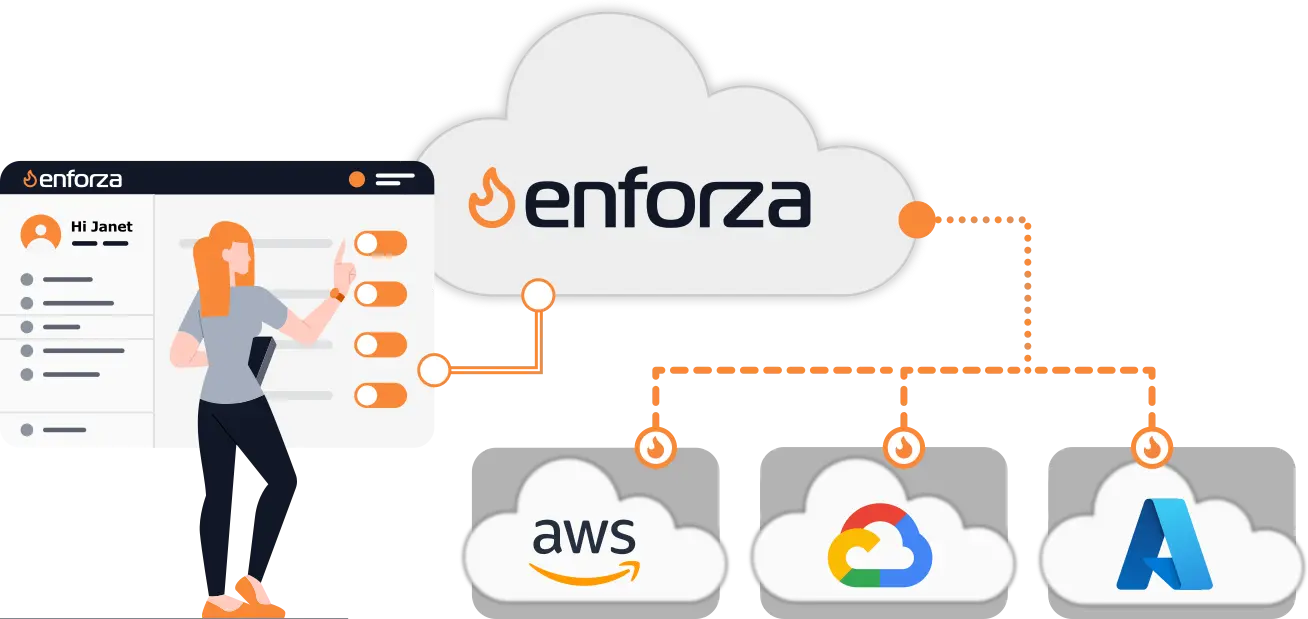
Replace your cloud-native Firewalls & NAT Gateways and save up to 80%. Centrally secure all your cloud workloads with a single pane of glass.
Deployable in minutes.
Latest Features & Updates
Continuously enhancing cloud security with powerful new capabilities and integrations.
Trusted by SMEs worldwide
- Cloud Regions Covered
- 30 +
- Gateways Provisioned
- 500 +
- Cost Savings
- ~ $1.2M












The Problem
The hidden complexity of cloud-native network security
Modern cloud platforms offer native firewalls and NAT gateways — but they’re expensive, inconsistent, and getting more restrictive. Default outbound internet access is being locked down, and maintaining secure, reliable network egress and ingress is becoming a costly engineering task.
From March 2026, new Azure virtual networks will no longer include default internet access. Outbound traffic will require a NAT Gateway, load balancer, or public IP — all of which incur extra costs (around $4/month per IP alone).
AWS and GCP already follow similar pricing models. What used to be free and simple now demands setup and adds hidden cost, even for basic tasks like updates or API calls.
- Cloud-native NATs are expensive and opaque. Usage-based billing and complex routing setups make it hard to control cost and predictability.
- Default internet access is disappearing. Azure, AWS, and GCP are phasing out free outbound internet by default — requiring explicit firewall or NAT configuration.
- Traditional firewalls are overkill for SMEs. Most small and mid-sized cloud environments don’t need full-blown security appliances — they just need safe, managed network policies.
The Solution
The enforza solution: Cloud-managed firewall & NAT without the overhead
enforza is a lightweight, cloud-controlled firewall and NAT gateway you can run on any VM — in AWS, Azure, GCP, or on-prem. Devices connect securely to the enforza control plane, receive rule updates in real time, and forward traffic safely under a simple usage model.
- Multi-cloud, single control plane. Manage outbound access, NAT, stateful firewalling, FQDN filtering, port forwarding, in any cloud from a simple cloud UI.
- Fixed pricing, no surprises: No GB data processing fees. No surprises. Control your costs, not just your traffic.
- Works anywhere. Deploy in minutes to any Linux VM using our simple client daemon — no cloud lock-in, no managed service traps.
“enforza helped us regain control of our cloud egress without spending hundreds per month on native NAT gateways. It just works.”
Whether you're a startup, a security-conscious dev team, or an SME needing predictable outbound access — enforza simplifies the problem with one lightweight agent and one clean policy model.
Your questions answered
Frequently asked questions
What is Enforza? +
Enforza is a secure NAT gateway and cloud firewall platform that gives you total control over your egress traffic. It enables FQDN-based filtering, logging, and central policy enforcement—all from a simple Linux-based appliance. Unlike managed cloud firewalls or NAT gateways, Enforza is fully self-hosted and designed for predictable cost and simplicity.
How does Enforza help reduce cloud costs? +
Enforza eliminates the need for costly managed NAT Gateways, VPC traffic mirroring, and proprietary firewall services. By replacing these with a lightweight, hardened Linux VM that handles both NAT and firewall duties, customers avoid hidden per-GB data processing charges. This leads to significant and predictable savings, especially at scale.
Does Enforza remove all data fees? +
Sadly not. We eliminated data processing charges on the cloud-native NAT Gateways and Firewalls. Data egress charges to the internet cannot be avoided when traffic is destined/sourced from the internet. However, all intra-cloud (east/west traffic) is not subject to data processing charges. Check out our Savings Calculator for a clear breakdown of charges.
Is Enforza a firewall or a secure NAT gateway? +
It’s both. Enforza acts as a stateful NAT device while also enforcing firewall rules, logging decisions, and performing FQDN-based access control. You no longer need to manage or chain separate NAT and firewall tools—it’s unified and policy-driven.
Is it cheaper than a cloud NAT gateway? +
Yes—often significantly. Even when used just for NAT, Enforza typically costs less than the managed NAT Gateway services provided by AWS, Azure, or GCP. And it provides more: logging, policy control, and observability come built-in, without extra charges.
How predictable are Enforza's costs? +
Very predictable. Since Enforza runs on a standard Linux VM or EC2 instance, your cost is based on that VM’s price—no additional per-flow, per-connection, or per-gigabyte fees. This means you can plan and budget without surprises.
Does Enforza scale with my infrastructure? +
Yes. You can deploy multiple Enforza nodes across regions, environments, or accounts. The Enforza Cloud Controller makes it easy to manage policies, monitor activity, and scale securely without adding operational complexity.
What kind of security does it provide? +
Enforza allows fine-grained control over outbound traffic using protocol, port, IP address, and FQDN-based filtering. Policies can be enforced centrally. Every connection decision is logged, making audits and forensics simple.
Is it stable, enterprise-ready and robust? +
Absolutely. Enforza is built using mature technologies that power the world’s largest cloud environments (basically, it's the same under the hood!). It’s hardened by default and tested in real-world production deployments.
Does it support encrypted traffic inspection? +
No. Enforza does not perform deep packet inspection (DPI) or TLS decryption. Instead, it focuses on metadata, FQDN filtering, and protocol-level control—ideal for environments where privacy, performance, and cost matter more than payload inspection.
How fast can I get started? +
Deployment takes just minutes. Spin up a Linux VM (or EC2 instance), copy the one-line install command from the Enforza Controller, and the device will register, self-configure, and become ready for policy deployment and telemetry streaming immediately.
Do I need to re-architect my cloud to use it? +
Not at all. Enforza works with existing VPCs and VNets. You can try it by simply updating a route table or UDR to point to your Enforza instance—no need to rewire or replatform. And removing it is just as easy.
Does Enforza log and analyze traffic? +
Yes. Every connection is logged with rich metadata. You can view traffic in real time via the Enforza Controller or export logs to your SIEM. Enforza also supports alerts on blocked traffic, DNS resolution failures, and suspicious behavior.
Can I push policy centrally? +
Yes. All devices connect back to the Enforza Cloud Controller. From there, you can build policies and push them out to any node, globally. Changes are atomic, audit-logged, and take effect immediately.
Is it compatible with AWS, Azure, and GCP? +
Yes. Enforza is completely cloud-agnostic. As long as your cloud platform allows you to launch a Linux instance and update a route table, Enforza works seamlessly. It supports public clouds, hybrid setups, and air-gapped environments.
Can it be white-labeled for MSPs or VARs? +
Yes. Enforza offers white-labeling options for managed service providers and value-added resellers. You can customize the branding, expose your own APIs, and embed Enforza into your service stack. Reach out to us for partnership options.
Is there special pricing for education, public sector, or NGOs? +
Yes—absolutely. We provide dedicated pricing tiers for educational institutions, public sector organizations, and registered non-profits. Just contact us with proof of eligibility and we’ll ensure you get discounted access.
How is Enforza different from traditional cloud firewalls? +
Traditional cloud firewalls are often expensive, limited to provider-specific tooling, and opaque in their behavior. Enforza is transparent, fully under your control, portable across clouds, and offers centralized policy enforcement—all at a lower cost.
What’s the risk in trying Enforza? +
Almost none. You don’t need to commit to architectural changes. Simply launch a VM, run the generated install command, push policy. Then the big switch is changing your route-table/UDR to point 0.0.0.0/0 to the vNIC/ENI - takes seconds. If you’re not happy, revert the route-table/UDR change (again, takes seconds) then delete the instance. No vendor lock-in.
Ditch the data processing charges.
Gain full control of your outbound traffic — in any cloud or on-prem.
